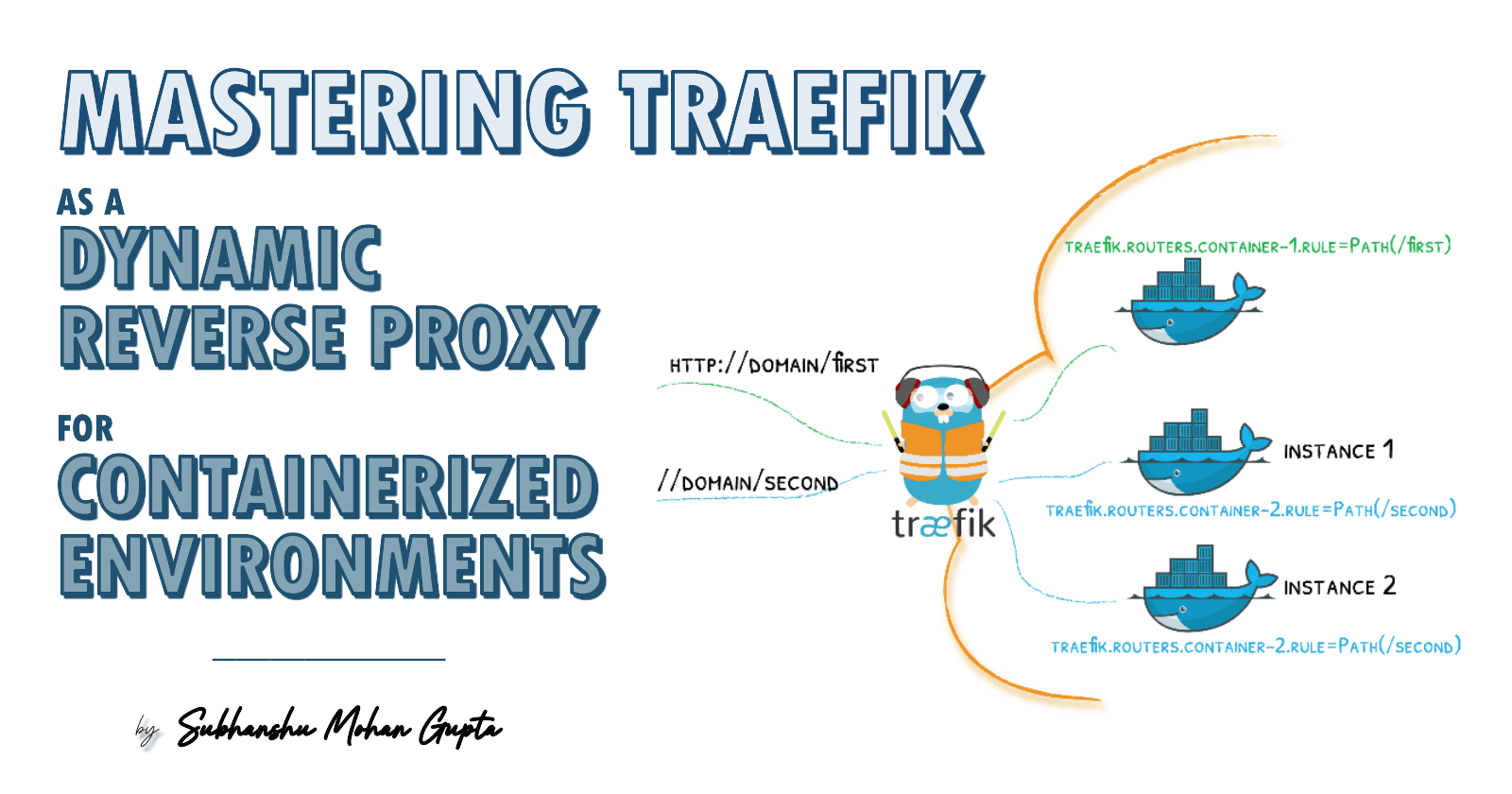
Mastering Traefik as a Dynamic Reverse Proxy for Containerized Environments
Auto-Scaling Your Microservices with Smart Reverse-Proxy Logic
A versatile DevSecOps Engineer specialized in creating secure, scalable, and efficient systems that bridge development and operations. My expertise lies in automating complex processes, integrating AI-driven solutions, and ensuring seamless, secure delivery pipelines. With a deep understanding of cloud infrastructure, CI/CD, and cybersecurity, I thrive on solving challenges at the intersection of innovation and security, driving continuous improvement in both technology and team dynamics.
Introduction
In modern microservices and containerized ecosystems, Traefik serves as a powerful reverse proxy, offering dynamic service discovery, advanced routing capabilities and automated SSL/TLS management through Let's Encrypt integration.
This article explores how to effectively configure and deploy Traefik in containerized environments, focusing on Docker-based implementations.
Core Components and Architecture
Dynamic Service Discovery
Traefik integrates natively with container orchestrators like Docker and Kubernetes, monitoring service lifecycles and automatically updating routing configurations. The Docker provider listens to container events and uses labels to configure routing rules, middleware, and load-balancing strategies.
Here's a foundational Docker container configuration:
version: '3.8'
services:
webapp:
image: myregistry/webapp:latest
labels:
- "traefik.enable=true"
- "traefik.http.routers.webapp.rule=Host(`webapp.example.com`)"
- "traefik.http.services.webapp.loadbalancer.server.port=80"
- "traefik.http.middlewares.webapp-rate-limit.ratelimit.average=100"
- "traefik.http.middlewares.webapp-rate-limit.ratelimit.burst=50"
networks:
- web
networks:
web:
external: true
Automated SSL/TLS Management
Traefik simplifies certificate management through Let's Encrypt integration. The ACME protocol handles certificate issuance, renewal, and management automatically. Here's the essential static configuration:
entryPoints:
web:
address: ":80"
websecure:
address: ":443"
providers:
docker:
endpoint: "unix:///var/run/docker.sock"
exposedByDefault: false
certificatesResolvers:
letsencrypt:
acme:
email: admin@example.com
storage: acme.json
httpChallenge:
entryPoint: web
Important security considerations:
Set strict permissions (600) on acme.json
Choose between HTTP and DNS challenges based on your infrastructure requirements
Traefik Architecture Overview
Source - https://traefik.io/traefik/

Advanced Features
Routing and Middleware Configuration
Traefik's routing system allows precise control over request handling through:
Path-based routing with rewriting capabilities
Header manipulation
Middleware chaining for enhanced security and control
Example of advanced routing configuration:
labels:
- "traefik.http.routers.api.rule=Host(`api.example.com`) && PathPrefix(`/v1`)"
- "traefik.http.routers.api.middlewares=api-stripprefix"
- "traefik.http.middlewares.api-stripprefix.stripprefix.prefixes=/v1"
Security and Rate Limiting
Traefik offers several middleware components for security:
Rate limiting to prevent abuse
IP whitelisting for access control
Circuit breakers to prevent cascade failures
Example rate limiting configuration:
labels:
- "traefik.http.middlewares.webapp-ratelimit.ratelimit.average=100"
- "traefik.http.middlewares.webapp-ratelimit.ratelimit.burst=50"
Production Deployment Guide
Complete Docker Compose Setup
This configuration demonstrates a production-ready Traefik deployment:
version: "3.7"
services:
traefik:
image: traefik:v2.10
container_name: traefik
restart: unless-stopped
command:
- "--log.level=DEBUG"
- "--api.insecure=false"
- "--providers.docker=true"
- "--providers.docker.exposedbydefault=false"
- "--entrypoints.web.address=:80"
- "--entrypoints.websecure.address=:443"
- "--certificatesresolvers.myhttpchallenge.acme.httpchallenge=true"
- "--certificatesresolvers.myhttpchallenge.acme.httpchallenge.entrypoint=web"
- "--certificatesresolvers.myhttpchallenge.acme.email=admin@example.com"
- "--certificatesresolvers.myhttpchallenge.acme.storage=/letsencrypt/acme.json"
- "--certificatesresolvers.myhttpchallenge.acme.tlschallenge=true"
ports:
- "80:80"
- "443:443"
volumes:
- "./letsencrypt:/letsencrypt"
- "/var/run/docker.sock:/var/run/docker.sock:ro"
labels:
- "traefik.enable=true"
# Traefik dashboard (secured)
- "traefik.http.routers.traefik-secure.entrypoints=websecure"
- "traefik.http.routers.traefik-secure.rule=Host(`monitor.example.com`)"
- "traefik.http.routers.traefik-secure.tls=true"
- "traefik.http.routers.traefik-secure.tls.certresolver=myhttpchallenge"
- "traefik.http.routers.traefik-secure.service=api@internal"
- "traefik.http.routers.traefik-secure.middlewares=traefik-auth"
- "traefik.http.middlewares.traefik-auth.basicauth.users=password:base64encodedpassword"
# catch-all HTTP → HTTPS
- "traefik.http.routers.http-catchall.rule=HostRegexp(`{host:[a-z-.]+}`)"
- "traefik.http.routers.http-catchall.entrypoints=web"
- "traefik.http.routers.http-catchall.middlewares=redirect-to-https"
- "traefik.http.middlewares.redirect-to-https.redirectscheme.scheme=https"
comtainer1:
image: image:latest
container_name: comtainer1
restart: unless-stopped
environment:
key: value
expose:
- "80"
volumes:
- volume1:/var/lib/volume1
labels:
- "traefik.enable=true"
# HTTP → HTTPS redirect
- "traefik.http.routers.container1-http.rule=Host(`container1.example.com`)"
- "traefik.http.routers.container1-http.entrypoints=web"
- "traefik.http.routers.container1-http.middlewares=redirect-to-https"
# HTTPS
- "traefik.http.routers.container1.rule=Host(`container1.example.com`)"
- "traefik.http.routers.container1.entrypoints=websecure"
- "traefik.http.routers.container1.tls=true"
- "traefik.http.routers.container1.tls.certresolver=myhttpchallenge"
- "traefik.http.services.container1.loadbalancer.server.port=80"
container2:
image: image:latest
container_name: container2
restart: unless-stopped
environment:
key: value
expose:
- "80"
volumes:
- volume2:/var/lib/volume2
labels:
- "traefik.enable=true"
- "traefik.http.routers.container2-http.rule=Host(`container2.example.com`)"
- "traefik.http.routers.container2-http.entrypoints=web"
- "traefik.http.routers.container2-http.middlewares=redirect-to-https"
- "traefik.http.routers.container2.rule=Host(`container2.example.com`)"
- "traefik.http.routers.container2.entrypoints=websecure"
- "traefik.http.routers.container2.tls=true"
- "traefik.http.routers.container2.tls.certresolver=myhttpchallenge"
- "traefik.http.services.container2.loadbalancer.server.port=80"
container3:
image: image:latest
container_name: container3
restart: unless-stopped
environment:
key: value
expose:
- "80"
volumes:
- volume3:/var/lib/volume3
labels:
- "traefik.enable=true"
- "traefik.http.routers.container3-http.rule=Host(`container3.example.com`)"
- "traefik.http.routers.container3-http.entrypoints=web"
- "traefik.http.routers.container3-http.middlewares=redirect-to-https"
- "traefik.http.routers.container3.rule=Host(`container3.example.com`)"
- "traefik.http.routers.container3.entrypoints=websecure"
- "traefik.http.routers.container3.tls=true"
- "traefik.http.routers.container3.tls.certresolver=myhttpchallenge"
- "traefik.http.services.container3.loadbalancer.server.port=80"
volumes:
volume1:
volume2:
volume3:
Dashboard interface of a running traefik container

Multi-Region and Multi-Cloud Deployments
For distributed deployments across regions or cloud providers:
Implement DNS-based global load balancing (using services like AWS Route 53 or Cloudflare)
Synchronize certificate storage across regions
Deploy region-specific Traefik instances with tailored configurations
Integrate with centralized logging and monitoring solutions
Best Practices
Always use explicit routing rules to prevent unintended exposure
Implement comprehensive middleware chains for security
Maintain separate configurations for development and production environments
Monitor Traefik's metrics and logs for operational insights
Regular backup of the certificate storage
Implement proper access controls for Traefik's API endpoints
Conclusion
Traefik stands out as a modern, lightweight and intelligent reverse proxy tailored for dynamic containerized environments. Its native integration with Docker and Kubernetes, automated service discovery, built-in SSL/TLS via Let's Encrypt and flexible middleware system make it a production-grade solution for managing microservices at scale. By following the implementation guide and best practices outlined in this article such as explicit routing, secure middleware configurations and automated certificate management, you can build a highly available, secure, and auto-scaling infrastructure.
Whether you're deploying in a single cloud, multi-region or hybrid-cloud environment, Traefik provides the agility and control needed to keep up with evolving DevOps demands and microservices architectures.
So embrace Traefik not just as a reverse proxy but as a dynamic orchestrator of service connectivity and reliability in your microservices landscape.