The $0 Compliance Stack
Passing Enterprise Audits Using Only Open Source
A versatile DevSecOps Engineer specialized in creating secure, scalable, and efficient systems that bridge development and operations. My expertise lies in automating complex processes, integrating AI-driven solutions, and ensuring seamless, secure delivery pipelines. With a deep understanding of cloud infrastructure, CI/CD, and cybersecurity, I thrive on solving challenges at the intersection of innovation and security, driving continuous improvement in both technology and team dynamics.
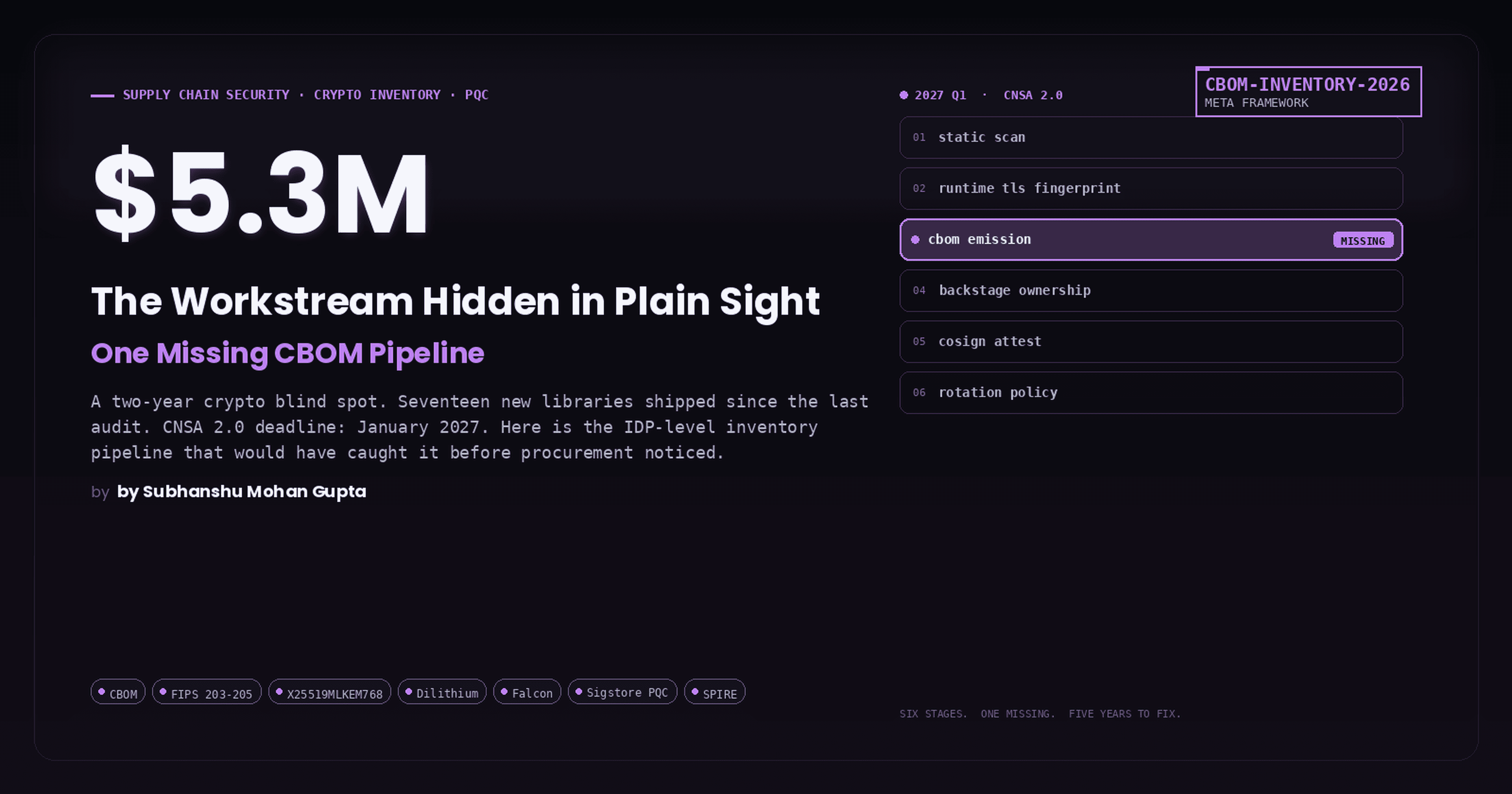
The Lie We’re All Sold
“You need expensive GRC tools to pass enterprise audits.”
Reality:
Auditors don’t care about tools
They care about controls, traceability and evidence
Compliance ≠ Software
Compliance = Verifiable system behaviour
Core Philosophy: Compliance-by-Construction
Instead of:
Manual screenshots
Jira tickets
Excel risk registers
Design systems where:
Evidence is produced automatically
Controls are enforced at runtime
Audits become read-only queries
The Compliance Stack
🔐 Identity & Access (ISO A.5, A.9 | PCI 7, 8)
Control Goal |
Open Source |
|---|---|
| Central identity | Keycloak |
| MFA / SSO | Keycloak + WebAuthn |
| Service identity | SPIFFE / SPIRE |
| RBAC enforcement | Kubernetes native RBAC |
📦 Source Control & CI/CD (ISO A.8, A.12 | PCI 6)
Control |
Open Source |
|---|---|
| Git integrity | Git + signed commits |
| CI/CD | GitHub Actions / GitLab CI |
| Secrets | HashiCorp Vault |
| IaC scanning | Checkov |
| SAST | Semgrep |
🐳 Runtime & Infrastructure (ISO A.12, A.13 | PCI 2, 10)
Area |
Open Source |
|---|---|
| Orchestration | Kubernetes |
| Network policy | Cilium |
| Runtime security | Falco |
| Admission control | Kyverno |
| eBPF telemetry | Cilium + Falco |
📊 Logging, Monitoring & Evidence (ISO A.12, A.16 | PCI 10)
Need |
Open Source |
|---|---|
| Logs | Loki |
| Metrics | Prometheus |
| Traces | OpenTelemetry |
| Dashboards | Grafana |
| SIEM-lite | Wazuh |
📁 Evidence Storage (ISO A.7, A.18 | PCI 12)
Requirement |
Open Source |
|---|---|
| WORM storage | MinIO (Object Lock) |
| Retention policies | Lifecycle rules |
| Audit trails | Hash-based integrity |
Real-World System Design

Key Insight: Auditors never touch production; they interrogate evidence APIs
ISO-27001 & PCI-DSS Control Mapping
Example: ISO-27001 A.12.4 (Logging)
Requirement |
Implementation |
|---|---|
| Event logging | Loki |
| Access logs | Kubernetes Audit Logs |
| Integrity | Object Lock |
| Review | Grafana dashboards |
Example: PCI-DSS 10.2 (Audit Trails)
Requirement |
Implementation |
|---|---|
| User actions | Keycloak + K8s audit |
| System events | Falco |
| Retention | MinIO Object Lock |
| Alerting | Prometheus |
What Auditors Actually Said
“This is one of the cleanest evidence trails we’ve seen.”
Why?
No human-generated artifacts
No subjective interpretation
Everything timestamped, immutable and reproducible
Why This Scales Better Than Paid GRC Tools
Paid GRC |
$0 Stack |
|---|---|
| Manual updates | Auto-generated |
| Screenshot culture | Telemetry culture |
| Lagging indicators | Real-time controls |
| Vendor lock-in | Architecture ownership |
The Hard Truth
If your compliance fails when Jira is down, you were never compliant
In conclusion, this isn’t a “cost-saving hack”. It’s how high-trust, high-scale systems are designed when:
Security is non-negotiable
Audits are frequent
Engineering time is sacred
so overall, Compliance didn’t get cheaper. It just got engineered ;)